Anti virus. Do I need it?
- Thread starter mekano
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
MarkHirt
Well-known member
- Feb 7, 2010
- 110
- 6
- 0
Do I need a app like Lookout or Advast? Some say yes some say no.
The people that say yes are for the most part those that want to sell you a Virus app
As stated above YOU are the best virus protection. Side loading a free hot porn stars app is probably not a good idea.
nelschroeder
Well-known member
- Dec 14, 2012
- 166
- 0
- 0
It's a personal comfort level....if it helps you sleep easier then fine. All the reputable antivirus apps are available in a free version....Norton, AVG, AVAST, Lockout....
Fairclough
Well-known member
- Nov 2, 2012
- 1,581
- 0
- 0
The only reason I would recommend one is for the free device trackers in it. E.g. avast with root install
- Android Central App. N'oublions jamais l'Australie, Villers-Bretonneux. Prepare for January 26.
- Android Central App. N'oublions jamais l'Australie, Villers-Bretonneux. Prepare for January 26.
moosc
Grand Master Moosc
- Oct 20, 2009
- 3,264
- 162
- 0
Wow so newbie. Google provides free tracking and remote wipe, Google has a built app scanner, Google uses its bouncer to check apps in playstore. If you want to feel warm and fuzzy use a third party av app designed for a pc. Also a search I bet this number topic brought up. So many scared people. Alas
http://qz.com/131436/contrary-to-what-youve-heard-android-is-almost-impenetrable-to-malware/
Contrary to what you?ve heard, Android is almost impenetrable to malware
By Steven Max Patterson October 3, 2013
Steven Max Patterson is a technology journalist and consultant to many software, electronics and renewable energy startups in Boston, San Francisco, and Europe.
Until now, Google hasn?t talked about malware on Android because it did not have the data or analytic platform to back its security claims. But that changed dramatically today when Google?s Android Security chief Adrian Ludwig reported data showing that less than an estimated 0.001% of app installations on Android are able to evade the system?s multi-layered defenses and cause harm to users. Android, built on an open innovation model, has quietly resisted the locked down, total control model spawned by decades of Windows malware. Ludwig spoke today at the Virus Bulletin conference in Berlin because he has the data to dispute the claims of pervasive Android malware threats.
Ludwig sees security in biological terms:
?A walled garden systems approach blocking predators and disease breaks down when rapid growth and evolution creates too much complexity. Android?s innovation from inside and outside Google are continuous, making it impossible to create such a walled garden by locking down Android at the device level.?
He stated Google?s mission in defending against malware in terms more closely akin to the Center for Disease Control (CDC) than the PC security industry.
?The CDC knows that it?s not realistic to try to eradicate all disease. Rather, it monitors disease with scientific rigor, providing preventative guidance and effective responses to harmful outbreaks.?
The problem Google wants to solve is that most independent security researchers don?t have access to a platform such as Google?s to measure how many times a malware app has been installed. They are analogous to human disease researchers without a CDC to measure the size of a disease outbreak and coordinate a response. Security researchers are very good at finding and fixing malware, but in the absence of reliable data that indicate how frequently a malware app has been installed, the threat level can become exaggerated. Reports that reach publication are often extremely exaggerated. To emphasize this point, Ludwig revealed in his analysis that some of the most publicized recent malware discoveries are installed in less than one per million installations.
A recent leaked report*(pdf) from the Department of Homeland Security (DHS) found that most Android malware was installed via text message. We?ve asked DHS to confirm its findings but have gotten no response at this time. This is what Ludwig had to say:
?An application that a user installs from a link within a text message would be included in these statistics [reported today in Berlin]. *Some of the short one to two day increases in ratio of installs per million apps can be attributed to text messaging or email spam campaigns.?
Contradicting these anecdotal reports, Ludwig?s analysis indicates that Android malware is not as significant a threat as has often been reported. Ludwig suggests that combining Google?s data driven approach with the research efforts of the industry will improve Android?s malware defenses going forward.
Google?s security mechanisms have improved Android?s malware defenses and provided Ludwig a platform for collecting and analyzing data from over 1.5 billion app installs. Google publicized its malware research results and explained its malware defense framework to invite industry review and broader participation.
The new security mechanisms appeared about a year ago when new versions of Android started shipping with Verify Apps. Verify Apps intervenes when an app is downloaded, compares it to a large database of malware information curated by Google and warns the user if the app is potentially harmful. Verify Apps is also distributed to older Android versions by including it in updates to the Google Play app that is used to download apps from Google?s app store. Checking and blocking apps is enabled by default requiring a user to choose to disable it in order to circumvent its protection.
Using Verify Apps, Google collected this data outside of the protected perimeter of the Google Play app store from installations ?in the wild? where the incidence of malware is higher. Based on the data from tracking over one and a half billion app installs Google obtained convincing evidence that the rate of ?potentially harmful apps? installed is stable at about 1,200 per million app installs, or about 0.12%. The classification ?potentially harmful apps? include both malware and false positive detections of malware. Often benign software apps have behaviors or characteristics resembling malware.
Verify Apps tracks each incident when a potentially hazardous app is flagged, when the user is warned, and when the user chooses to ignore the warning and installs the app. Warnings are an effective deterrent to malware. Only 0.12% of users chose to ignore the warnings and install potentially hazardous apps.
The research presented by Ludwig includes the classification of the types of threats that are represented in a sample of the 1,200 potentially harmful apps installed per million.
Almost 40% are ?fraudware? apps that drain the users smartphone account by making premium telephone calls or sending premium SMS messages.
Another 40% classified as ?rooting? apps are labeled as potentially harmful applications by Verify Apps, but they are not considered malicious. Smartphone hobbyists and developers frequently root their devices for many benign reasons such as installing custom Android versions like CyanogenMod or to remove carrier installed apps.
About 15% of the apps flagged by Verify Apps are commercial spyware, a diverse set of monitoring apps that range from tracking internet behavior to improve advertising to the very malicious keyloggers that collect personal information entered by the user and report it to the malware creator. The 6% balance is a diverse set of mainly malicious apps.
This framework for improving Android?s malware defenses is an extension of the open innovation model that made Android successful. Publishing Android source code for public review has improved Android beyond even Google?s resource limits by subjecting it to the review of independent software developers. An example of this is the National Security Agency?s (NSA) research project to enhance Android security named SE-Android*(pdf), which has contributed research and software that was merged into recent releases of Android. It?s an insightful example of the power of open innovation because much of the security technology came from another open source innovation project to enhance the security of Linux. Despite public suspicion about NSA surveillance, SE Android is not a surveillance risk because like Android it is completely open to public review.
A locked down *approach has worked for Apple in protecting iOS from malware because it controls both hardware and software towards the goal of maximizing its profits. In contrast Google has used an open model to maximize Android market share in which it licenses Android for free and controls neither the hardware or software ultimately sold to the end customer. This model has allowed for rapid innovation that resulted in a large market share but has created the need for the open malware defense framework that Ludwig presented.
Ludwig invited the industry to ?raise the bar? from here using more and better data to analyze the threat to the user and respond with more effective measures. Coming from Google, this should be no surprise given its obsession with big data and analytics. Open innovation and open source has helped Android achieve market dominance. According to IDC, Android won 79% of the smartphone market share in the second quarter of 2013. Ludwig makes a convincing data driven case that Android is secure?now we?ll see whether Google can make similar gains in Android security that it has made in market share.*
Sent from Bad Azz VZW LG G2 Cyan Tapatalk
http://qz.com/131436/contrary-to-what-youve-heard-android-is-almost-impenetrable-to-malware/
Contrary to what you?ve heard, Android is almost impenetrable to malware
By Steven Max Patterson October 3, 2013
Steven Max Patterson is a technology journalist and consultant to many software, electronics and renewable energy startups in Boston, San Francisco, and Europe.
Until now, Google hasn?t talked about malware on Android because it did not have the data or analytic platform to back its security claims. But that changed dramatically today when Google?s Android Security chief Adrian Ludwig reported data showing that less than an estimated 0.001% of app installations on Android are able to evade the system?s multi-layered defenses and cause harm to users. Android, built on an open innovation model, has quietly resisted the locked down, total control model spawned by decades of Windows malware. Ludwig spoke today at the Virus Bulletin conference in Berlin because he has the data to dispute the claims of pervasive Android malware threats.
Ludwig sees security in biological terms:
?A walled garden systems approach blocking predators and disease breaks down when rapid growth and evolution creates too much complexity. Android?s innovation from inside and outside Google are continuous, making it impossible to create such a walled garden by locking down Android at the device level.?
He stated Google?s mission in defending against malware in terms more closely akin to the Center for Disease Control (CDC) than the PC security industry.
?The CDC knows that it?s not realistic to try to eradicate all disease. Rather, it monitors disease with scientific rigor, providing preventative guidance and effective responses to harmful outbreaks.?
The problem Google wants to solve is that most independent security researchers don?t have access to a platform such as Google?s to measure how many times a malware app has been installed. They are analogous to human disease researchers without a CDC to measure the size of a disease outbreak and coordinate a response. Security researchers are very good at finding and fixing malware, but in the absence of reliable data that indicate how frequently a malware app has been installed, the threat level can become exaggerated. Reports that reach publication are often extremely exaggerated. To emphasize this point, Ludwig revealed in his analysis that some of the most publicized recent malware discoveries are installed in less than one per million installations.
A recent leaked report*(pdf) from the Department of Homeland Security (DHS) found that most Android malware was installed via text message. We?ve asked DHS to confirm its findings but have gotten no response at this time. This is what Ludwig had to say:
?An application that a user installs from a link within a text message would be included in these statistics [reported today in Berlin]. *Some of the short one to two day increases in ratio of installs per million apps can be attributed to text messaging or email spam campaigns.?
Contradicting these anecdotal reports, Ludwig?s analysis indicates that Android malware is not as significant a threat as has often been reported. Ludwig suggests that combining Google?s data driven approach with the research efforts of the industry will improve Android?s malware defenses going forward.
Google?s security mechanisms have improved Android?s malware defenses and provided Ludwig a platform for collecting and analyzing data from over 1.5 billion app installs. Google publicized its malware research results and explained its malware defense framework to invite industry review and broader participation.
The new security mechanisms appeared about a year ago when new versions of Android started shipping with Verify Apps. Verify Apps intervenes when an app is downloaded, compares it to a large database of malware information curated by Google and warns the user if the app is potentially harmful. Verify Apps is also distributed to older Android versions by including it in updates to the Google Play app that is used to download apps from Google?s app store. Checking and blocking apps is enabled by default requiring a user to choose to disable it in order to circumvent its protection.
Using Verify Apps, Google collected this data outside of the protected perimeter of the Google Play app store from installations ?in the wild? where the incidence of malware is higher. Based on the data from tracking over one and a half billion app installs Google obtained convincing evidence that the rate of ?potentially harmful apps? installed is stable at about 1,200 per million app installs, or about 0.12%. The classification ?potentially harmful apps? include both malware and false positive detections of malware. Often benign software apps have behaviors or characteristics resembling malware.
Verify Apps tracks each incident when a potentially hazardous app is flagged, when the user is warned, and when the user chooses to ignore the warning and installs the app. Warnings are an effective deterrent to malware. Only 0.12% of users chose to ignore the warnings and install potentially hazardous apps.
The research presented by Ludwig includes the classification of the types of threats that are represented in a sample of the 1,200 potentially harmful apps installed per million.
Almost 40% are ?fraudware? apps that drain the users smartphone account by making premium telephone calls or sending premium SMS messages.
Another 40% classified as ?rooting? apps are labeled as potentially harmful applications by Verify Apps, but they are not considered malicious. Smartphone hobbyists and developers frequently root their devices for many benign reasons such as installing custom Android versions like CyanogenMod or to remove carrier installed apps.
About 15% of the apps flagged by Verify Apps are commercial spyware, a diverse set of monitoring apps that range from tracking internet behavior to improve advertising to the very malicious keyloggers that collect personal information entered by the user and report it to the malware creator. The 6% balance is a diverse set of mainly malicious apps.
This framework for improving Android?s malware defenses is an extension of the open innovation model that made Android successful. Publishing Android source code for public review has improved Android beyond even Google?s resource limits by subjecting it to the review of independent software developers. An example of this is the National Security Agency?s (NSA) research project to enhance Android security named SE-Android*(pdf), which has contributed research and software that was merged into recent releases of Android. It?s an insightful example of the power of open innovation because much of the security technology came from another open source innovation project to enhance the security of Linux. Despite public suspicion about NSA surveillance, SE Android is not a surveillance risk because like Android it is completely open to public review.
A locked down *approach has worked for Apple in protecting iOS from malware because it controls both hardware and software towards the goal of maximizing its profits. In contrast Google has used an open model to maximize Android market share in which it licenses Android for free and controls neither the hardware or software ultimately sold to the end customer. This model has allowed for rapid innovation that resulted in a large market share but has created the need for the open malware defense framework that Ludwig presented.
Ludwig invited the industry to ?raise the bar? from here using more and better data to analyze the threat to the user and respond with more effective measures. Coming from Google, this should be no surprise given its obsession with big data and analytics. Open innovation and open source has helped Android achieve market dominance. According to IDC, Android won 79% of the smartphone market share in the second quarter of 2013. Ludwig makes a convincing data driven case that Android is secure?now we?ll see whether Google can make similar gains in Android security that it has made in market share.*
Sent from Bad Azz VZW LG G2 Cyan Tapatalk
Last edited:
John Doe40
Well-known member
- Aug 17, 2013
- 45
- 0
- 0
Do I need a app like Lookout or Advast? Some say yes some say no.
Opinions please? If yes which one? Should I pay for it or is free one good enough?
Posted via Android Central App
Free versions are good enough, the paid versions only add extra features like tracking or remote wipe and such... As to whether you "need" one - it's up to you to decide. If you only download apps from Google Play - you have less chance of getting some spyware or other malware, HOWEVER you still have a chance of getting one even from Google's own store. I'd say try it out - good antivirus apps take very little system resources, same goes for battery life. If you won't like it - you can always uninstall it.
I got wacked by a virus on my ACL on my HP Touchpad. It got on via Openmobile or a bogus Amazon app store.
Trust no one. If you feel you need one, get it from a company that offers a free version. If they don't, then they are a scam.
Posted via Android Central App
Trust no one. If you feel you need one, get it from a company that offers a free version. If they don't, then they are a scam.
Posted via Android Central App
If you know nothing about operating systems, files, executables, permissions and such things then yes, I'd recommend you install an AV...
Now, if you know what you are doing, and do not install an app that requires strange permissions on your phone, then no, you do not need anything else...
The same goes with web browsing...
Now, if you know what you are doing, and do not install an app that requires strange permissions on your phone, then no, you do not need anything else...
The same goes with web browsing...
NexusNick123
Well-known member
- Nov 11, 2013
- 313
- 0
- 0
I have on all my Android device my Nexus 7&5 just to be safe but if you download apps from the play store and keep it safe you should be fine. but if you want to download one it won't hurt
moosc
Grand Master Moosc
- Oct 20, 2009
- 3,264
- 162
- 0
Actually not quite true. Some av apps can cause system lag, use extra battery etc. But if it makes u feel warm n fuzzy then that is all that matters.
Sent from Bad Azz VZW LG G2 Cyan Tapatalk
I have on all my Android device my Nexus 7&5 just to be safe but if you download apps from the play store and keep it safe you should be fine. but if you want to download one it won't hurt
Sent from Bad Azz VZW LG G2 Cyan Tapatalk
The people that say yes are for the most part those that want to sell you a Virus app
I agree. I've not seem much if any evidence of viruses on Android being a problem except from antivirus companies.
mrsmumbles
Well-known member
- Oct 5, 2013
- 4,281
- 6
- 38
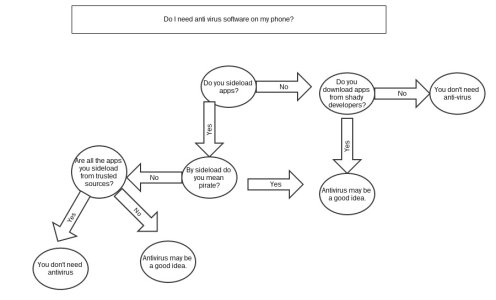
I have a handy flowchart for this!
View attachment 96959
The problem is not knowing if a Dev is shady.
Sent from my LG870 via Tapatalk 2
The only antivirus anyone needs on their phone is called Common Sense. Unfortunately, it's not as ubiquitous as it should be.
Can't help but agree.
gp8.3
BlackedOutLT1
Well-known member
- Sep 28, 2012
- 51
- 0
- 0
techitrucker
Well-known member
- Jul 7, 2012
- 270
- 0
- 0
The most important thing good security software does on Android is let you know if the software your installing has links to sites that are known for stealing information, what its really using those permissions for and whether that link you clicked is going to take you someplace that could be regrettable, all things that use little to no resources on your device and all problems that are regrettably common on all operating systems. Its amazing the things that seemingly legitimate programs from reputable companies on the Play Store do so they can sell your information yet no one calls them out on it. Though it is true that the chances of getting and actual virus on your device if using the Play Store are vanishingly small, it is only the smallest part of what reputable security software does. Active scanning for things like viruses is not necessary on sand boxed OS's like Android but they are not the real threat for most people. What good software does is keep you from installing apps that you are giving free permission to steal your information thereby defeating the sand box and keeping you away from dangerous sites you may not know are dangerous. What the good ones do is remind you to be mindful of your own security. In a perfect world everyone would read every permission for every app they download. In the real world how many people really do that and even if they do, how do they know what web sites any given program is affiliated with? Extra security done in a reasonable manner is never a bad idea no matter what os. The best ones on Android are mostly free.
Posted via Android Central App
Posted via Android Central App
Trending Posts
-
Question Crobo Promo Code [[315db33g]]: Get $25 FREE on Every Transaction
- Started by oggy88
- Replies: 0
-
Crobo Promo Code [["51k3b0je"]] Get $25 FREE on Every Transaction
- Started by oggy88
- Replies: 0
-
-
-
Forum statistics
Space.com is part of Future plc, an international media group and leading digital publisher. Visit our corporate site.
© Future Publishing Limited Quay House, The Ambury, Bath BA1 1UA. All rights reserved. England and Wales company registration number 2008885.